When Generic Threat Intelligence Isn’t Enough
Not all cybersecurity challenges are created equal.
A retail company managing phishing risks and a national defense agency operate in fundamentally different threat environments. The tools they use and the intelligence they require should reflect that.
For governments, military units, and intelligence agencies, the stakes of a missed vulnerability aren’t measured in financial loss alone. They’re measured in national security, critical infrastructure integrity, and sovereign cyber capability. That level of responsibility demands a different class of intelligence. A solution that is vetted, mission-ready, and built exclusively for authorized national security stakeholders.
That’s exactly what zIntel© was built to deliver.
What is zIntel©?
zIntel© is Zerotak’s proprietary Zero-Day Intelligence Portal. A restricted platform designed specifically for governments, defense organizations, military units, and intelligence agencies.
Its purpose is clear: to provide vetted zero-day and threat intelligence that helps national security stakeholders protect critical infrastructure and develop authorized cyber capabilities.
This is not a commercial SaaS product available to the general market. Access to zIntel© is intentionally restricted and granted exclusively to approved government entities. It ensures that the intelligence shared on the platform remains sensitive, trusted, and relevant to those with the mandate to act on it.
The Intelligence zIntel© Provides
At the core of zIntel© is a curated, continuously growing database of verified intelligence records. Each one is analyzed and validated before being made available on the platform.
Zero-Day Vulnerability Intelligence
zIntel© delivers 0-day exploits to government entities in the form of structured intelligence, ready to be used either for protecting national critical infrastructure or for enhancing authorized cyber capabilities.
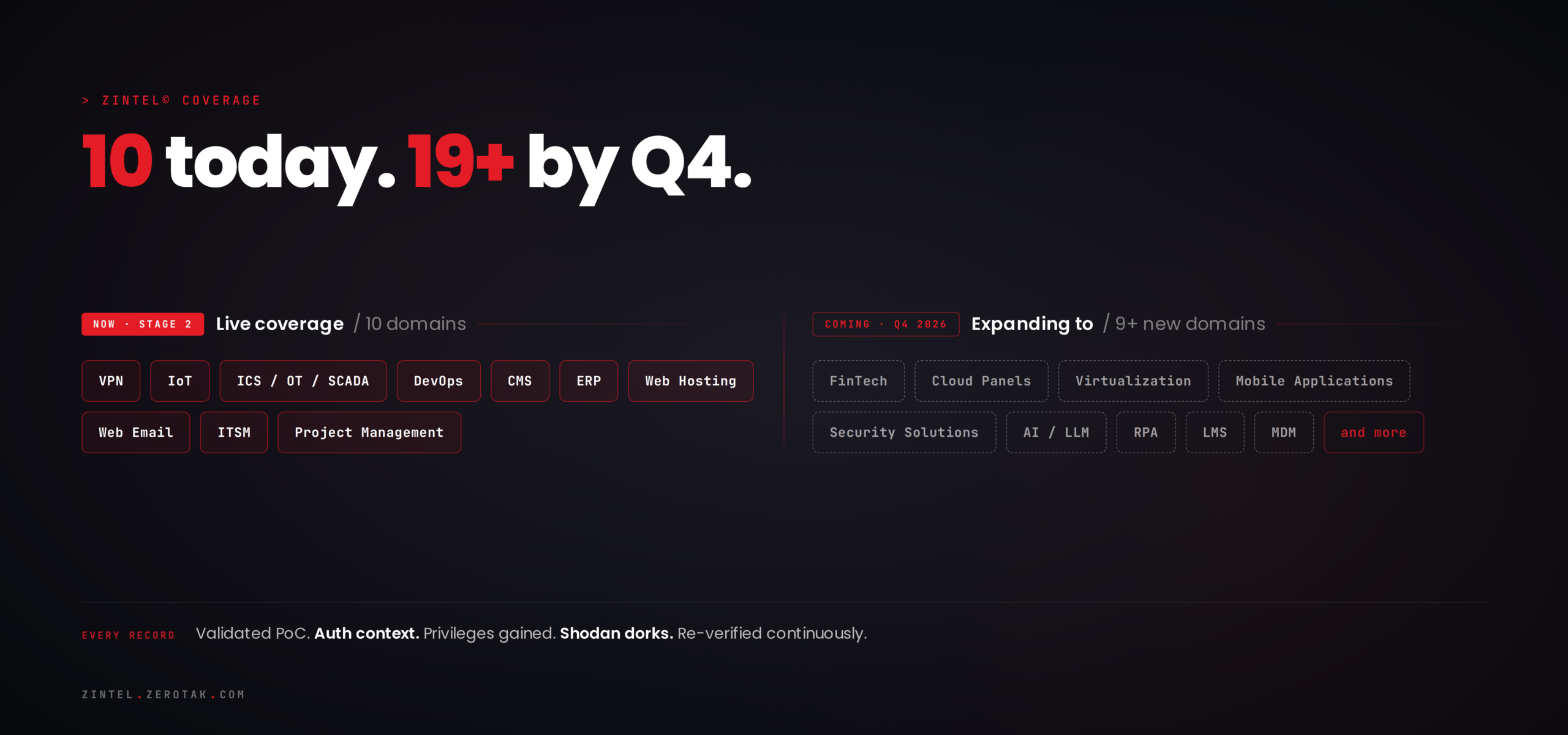
What sets this apart from conventional vulnerability disclosure is the operational depth behind each record. Every zero-day on the platform is manually validated against its target solution before being made available. Each record is delivered ready-to-use, and is continuously maintained periodically re-verified to confirm it remains current and exploitable. This way intelligence consumers can trust what they’re acting on. Each intelligence record includes a fully contextualized Proof-of-Concept (PoC), structured around the information that operational teams actually need: Authentication Context (Pre-Auth or Post-Auth), Privileges Gained (e.g., root, SYSTEM, admin), Environment Context and Shodan Dorks.
Shodan Dorks are curated search queries shipped with every record. They reveal real-world exposure instantly; how many systems are still vulnerable, where, and at what scale. Because zIntel© only covers technologies actively deployed on the internet, every dork translates directly into operational reality.
Multi-Domain Coverage
zIntel©‘s intelligence records span a wide and growing range of technology domains. Current coverage includes:
- VPNs : critical remote access infrastructure
- Web Hosting & Web Email : widely deployed, widely targeted
- IoT : increasingly prevalent in both civilian and defense environments
- ICS / OT / SCADA : industrial control systems and operational technology
- DevOps tooling : CI/CD pipelines and development infrastructure
- CMS platforms : content management systems used across government web presence
- ERP systems : enterprise resource planning platforms handling sensitive operational data
- ITSM & Project Management tools : internal workflow and service management platforms
This coverage is expanding. By Q4 2026, zIntel©‘s roadmap includes intelligence records across additional high-value categories, including FinTech, Cloud Panels, Virtualization, Mobile Applications, Security Solutions, AI/LLM systems, RPA, LMS, and MDM platforms.
The Platform: From Trusted Intelligence to Operational Capability
zIntel© is built around a single operational philosophy: trusted intelligence should translate directly into operational capability.
The platform brings together everything a national security team needs in one secure environment. Zero-day insights, real-time threat context, affected technology mapping, and PoC resources. No fragmented toolsets. No context-switching. Just a unified intelligence hub designed for mission-critical use.
Access Tiers
zIntel© offers two access tiers, both restricted to approved government entities:
Standard Tier includes:
- Full dashboard access
- API access for integration with existing security infrastructure
- Customer support
- Post-Authentication exploit intelligence
Premium Tier extends Standard with:
- Pre-Authentication exploit intelligence (higher-sensitivity records covering the most critical attack vectors)
- Custom intelligence requests (tailored to operational requirements, threat scenarios, or technology environments)
The distinction between tiers isn’t just about volume of records. Pre-Auth exploits represent the most dangerous class of vulnerabilities. Those that require no credentials to execute. We also supports custom requests allowing organizations to commission tailored records based on specific technologies, threat scenarios, or operational requirements outside the standard catalog.
Where zIntel© Stands Today: The Roadmap
zIntel© is an active, evolving platform. Here’s where it currently stands:
Stage 1 : Passed
- Platform fully developed
- Security mechanisms implemented and tested
Stage 2 : Current
- 30+ verified intelligence records added
- 10 technology category domains covered
- Platform testing and initial record onboarding are complete
Stage 3 : Expected Q4 2026
- 100+ verified records to be added
- Coverage expansion into FinTech, Virtualization, Cloud Panels, Mobile Applications, Security Solutions, AI/LLM, RPA, LMS, MDM, and more
Final Stage : 2027 and Ongoing
- Active rolling addition of new intelligence records
- Ongoing customer support for custom intelligence requests
- Continuous validation and verification of all records to ensure accuracy and operational relevance
This roadmap reflects Zerotak’s commitment to building zIntel© as a long-term intelligence resource. Not a one-time product launch, but a continuously maintained and expanded capability.
Why This Matters: The Case for Dedicated Government Zero-Day Intelligence
Zero-day vulnerabilities are among the most consequential assets in cyber operations.
0day in the VPN system? -> Initial Access Granted.
0day in the ICS/SCADA/OT system? -> Powergrid is offline.
0day in a framework that is used for government applications? -> Personal information of millions of people exposed
The challenge for government security teams is that:
- Generic commercial threat feeds are not designed with national security use cases in mind
- Public vulnerability databases only contain information once a vulnerability is disclosed, often after it has already been exploited
- Custom intelligence requirements specific to a nation’s technology stack or threat landscape; cannot be met by off-the-shelf solutions
zIntel© addresses each of these gaps directly. Its records are vetted and validated before distribution. Its access model ensures intelligence does not leak beyond authorized recipients. Its custom request capability means organizations can obtain intelligence tailored to their specific operational environment.
Built by Practitioners, for High-Stakes Operations
Zerotak is a team of ethical hackers, penetration testers, and cybersecurity professionals with certifications including OSCE3, OSCP, CREST CRT, and CEH. We also have a track record of working with organizations across Europe and the Middle East.
zIntel© is not the product of a software team that pivoted into security. It was built by people who conduct real penetration tests against the same technologies covered in the platform’s intelligence records. A team that understands not just that a vulnerability exists, but how an adversary would realistically exploit it, and what a defender needs to respond effectively.
That practitioner depth is embedded in every aspect of the platform. From how records are structured, to how exploit types are categorized, to the PoC resources provided for authorized validation.
Access zIntel©
zIntel© is a restricted platform. Access is not open to the public and is granted exclusively to approved government entities. We’re talking about defense organizations, military units, intelligence agencies, and authorized national cyber authorities.
If your organization operates within this industry and you are evaluating zero-day intelligence solutions, zIntel© is designed for you.
Explore the platform at zintel.zerotak.com
For access inquiries and eligibility verification: zintel@zerotak.com

![[BUN] zerotak_zintel_banner (1) (1)](https://zerotak.com/wp-content/uploads/2026/05/BUN-zerotak_zintel_banner-1-1-1-scaled.png)